

Security Audit
- Category: Penetration Testing
- Standards followed: PTES, OSSTMM, OSINT, NIST, OWASP
- Services Brochure: Download
Penetration Testing
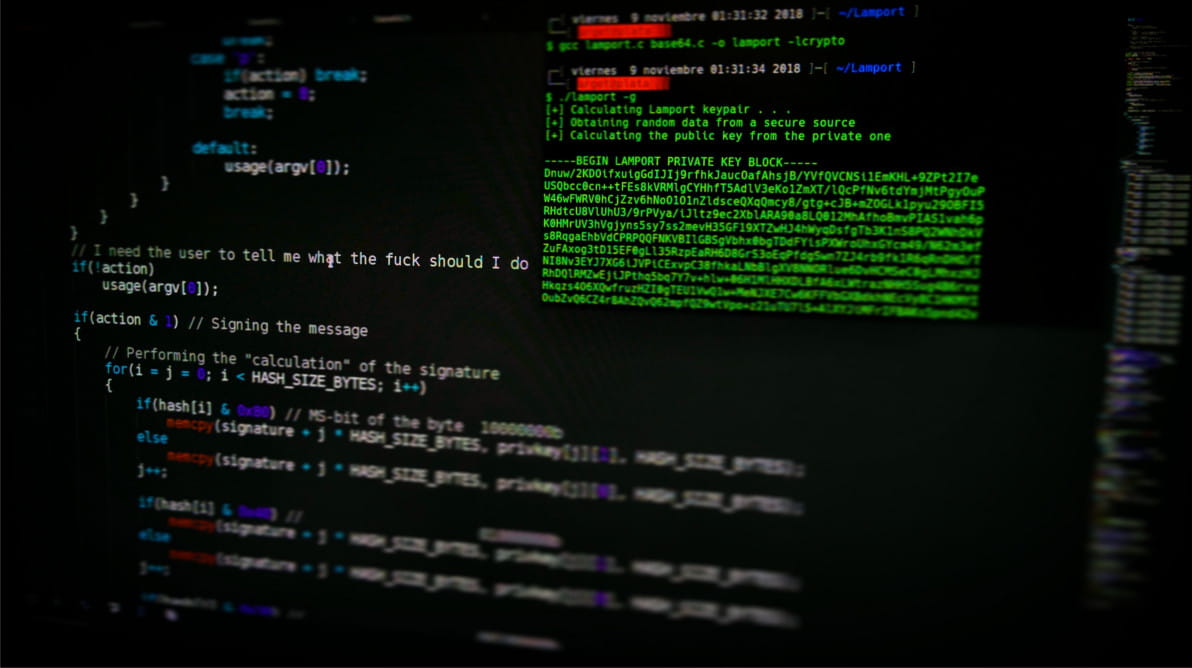
Pentesting is the art of exploiting weakness and vulnerabilities in a network. Pentest is performed considering the perspective of an outside attacker or a malicious insider. Gaps might exist in any environment, including the most secure ones. Pentesting is not just the need but also helps in remaining compliant with leading certifications like PCI, GDPR, etc.
Every organization has different requirements and a different working state. Our team at Alpha Threat understand this and therefore consider the approach that suits your organization the best.
Types of Penetration Testing:
Our team of experts use the exact methodology as that of real world attackers. Automated and Manual assessments are performed to unveil all the underlying flaws and loopholes. The vulnerabilities found are then used to initiate an outbound connection from the company's network as a proof of concept. No data leaves the organization in the process. The methods used by the experts not only strengthen the hold in the network but also to test the organization's ability to mitigate a realtime threat.
All the tests are performed under a Non Disclosure Agreement.
BENEFITS OF PENETRATION TESTING
Reveal real exploitable vulnerabilities
A high risk vulnerability might not be risky due to the difficulty level of exploitation. This analysis requires specialist. A pentest helps to sort out most critical vulnerabilities that need to be patched first.
Ensure Business continuity
A penetration test is required to reveal potential threats like server crash, DoS attacks, etc that can cause downtime in business, therefore ensuring business continuity
Maintain Compliance
Audits like ISO 27001 and PCI regulations requires compliance by maintaining regular Vulnerability Assessment and Penetration testing audit activity
Test your defense capability
Put your security team and mechanisms to test. Actions taken by your security team and the installed security systems determine the security level of your infrastructure
DELIVERABLE
The key delieverable from the testing includes a detailed report explaining:
Vulnerabilities are risk ranked to prioritised remediation.
QUICK LINKS
Contact
Got Questions? We are just an email away!
